- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: strftime() showing different time
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
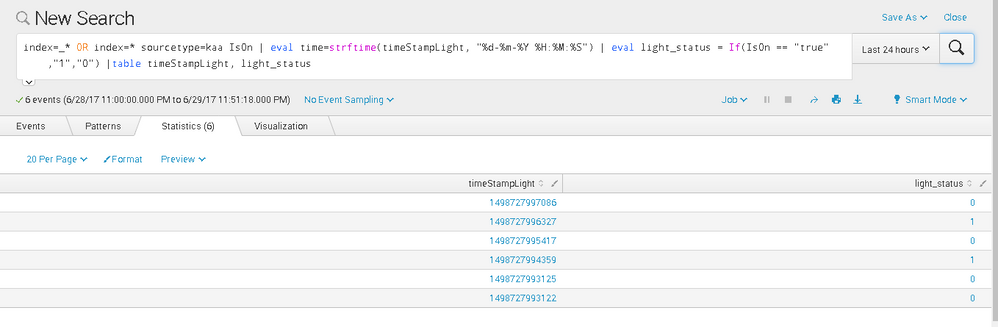
I converted my timeStampLight with strftime() but all my time was formatted to 31-12-9999 23:59:59 when I table time .
My timeStampLight is actually showing Epoch time format when I table timeStampLight. The format "%d-%m-%Y %H:%M:%S" should be correct as I managed to get my timestamp for the other log.
Any idea what went wrong with this one??
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi wuming79,
what is your timeStampLight value?
try to divide by 1000 and then apply strftime.
| eval timeStampLight=strftime(timeStampLight/1000,"%d-%m-%Y %H:%M:%S")
Bye.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It looks like your timeStampLight field isn't actually an epochtime value (seconds since the epoch), but rather milliseconds since the epoch, ie epochtime*1000. So @cusello's suggestion to divide by 1000 before strftime should work for you.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
ah thanks!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi wuming79,
what is your timeStampLight value?
try to divide by 1000 and then apply strftime.
| eval timeStampLight=strftime(timeStampLight/1000,"%d-%m-%Y %H:%M:%S")
Bye.
Giuseppe