Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Splunk Search
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- How to separate out basic search of Splunk in two ...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How to separate out basic search of Splunk in two different columns?
AjayTakur
Loves-to-Learn Everything
04-26-2023
12:34 PM
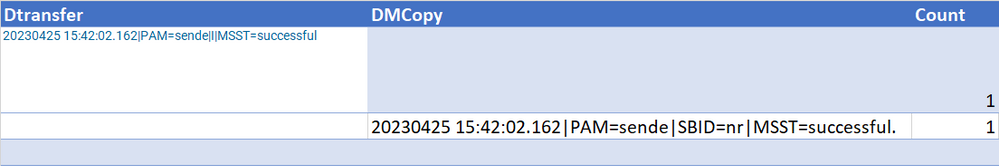
I am new to Splunk and facing an issue in separating out the two columns of the query. I tried with the below query and found the results as shown below in table1
...| append [search index="pd" "successful" "notif/output/" | stats count by _raw |fields count | rename _raw as Dtransfer] | append [search index="pd" "SBID=nr" "DM" "PAM=sende" "notif/archive/" | stats count by _raw |fields count | rename _raw as DMCopy]
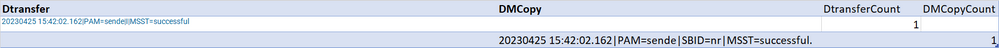
How do I achieve the expected result shown in Table 2? I need to display two separate columns DtransferCount and DMCopyCount
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
richgalloway

SplunkTrust
04-26-2023
01:09 PM
Specify the name of the count field in the stats commands.
...|
append [search index="pd" "successful" "notif/output/" | stats count as DtransferCount by _raw |fields DtransferCount | rename _raw as Dtransfer] |
append [search index="pd" "SBID=nr" "DM" "PAM=sende" "notif/archive/" | stats count as DDMCopyCount by _raw |fields DDMCopyCount | rename _raw as DMCopy]
---
If this reply helps you, Karma would be appreciated.
If this reply helps you, Karma would be appreciated.
Get Updates on the Splunk Community!
Everything Community at .conf24!
You may have seen mention of the .conf Community Zone 'round these parts and found yourself wondering what ...
Index This | I’m short for "configuration file.” What am I?
May 2024 Edition
Hayyy Splunk Education Enthusiasts and the Eternally Curious!
We’re back with a Special ...
New Articles from Academic Learning Partners, Help Expand Lantern’s Use Case Library, ...
Splunk Lantern is a Splunk customer success center that provides advice from Splunk experts on valuable data ...