- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Help with field extraction regex
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
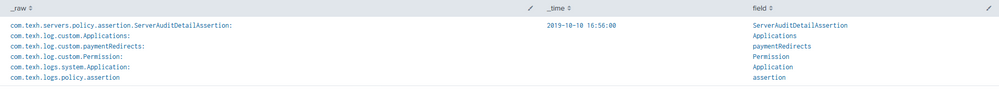
- com.texh.servers.policy.assertion.ServerAuditDetailAssertion:
com.texh.log.custom.Applications:
com.texh.log.custom.paymentRedirects:
com.texh.log.custom.Permission:
com.texh.logs.system.Application:
com.texh.logs.policy.assertion:
| rex field=_raw "^(?:[^ \n]* ){6}(?P[^ ]+)" and "^(.\w*?):"
I tried above but it's not correct.
I need to extract these: ServerAuditDetailAssertion, Applications paymentRedirects Permission Application assertion to any new field.
Can someone help me with this?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This regex will accomplish that. Here's a run anywhere example as well to demonstrate it: | rex field=_raw max_match=0 "com\..*\.(?<field>[^\:]+)"
| makeresults count=1
| eval _raw="com.texh.servers.policy.assertion.ServerAuditDetailAssertion:
com.texh.log.custom.Applications:
com.texh.log.custom.paymentRedirects:
com.texh.log.custom.Permission:
com.texh.logs.system.Application:
com.texh.logs.policy.assertion"
| rex field=_raw max_match=0 "com\..*\.(?<field>[^\:]+)"
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This regex will accomplish that. Here's a run anywhere example as well to demonstrate it: | rex field=_raw max_match=0 "com\..*\.(?<field>[^\:]+)"
| makeresults count=1
| eval _raw="com.texh.servers.policy.assertion.ServerAuditDetailAssertion:
com.texh.log.custom.Applications:
com.texh.log.custom.paymentRedirects:
com.texh.log.custom.Permission:
com.texh.logs.system.Application:
com.texh.logs.policy.assertion"
| rex field=_raw max_match=0 "com\..*\.(?<field>[^\:]+)"
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@dmarling Thanks, I got it.
This one worked
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Can you please clarify exactly what output you want? I've read your question, but I'm not sure what you are trying to do. Are there values after the colon? Are you looking for one field or multiple?
Could you maybe list the exact log message (anonymity, but have representative data in its place) with a table of field and expect value. There are many regex gurus here, but to me at least its not clear what you are requesting.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello @triest , I just need the regex one. I am looking for extracting a field starting with "com." and last word before ":"
"com.....assertion:" I just want to do stats of field extracted from a word before colon.
eg:
My events: (are not indexed correctly)
com.texh.logs.policy.assertion: 0880
com.texh.log.custom.exemptions:
com.texh.log.custom.payment: 8800:
com.texh.log.call.Permission: ABCD: dshhvnk dndsvndskjvdscn: jdcnvfdkjvnfdkv:
com.texh.logs.system.Application: 8877:
If i do | rex field=_raw max_match=0 ".(?[^.]+):\s+\d+:" | stats count by foo it is not extracting all fields
My results should be:
foo count
assertion 10
excemptions 20
Payment 30
Permission 40
Application 50
To my understanding
index=test sourcetype=test
| rex field=_raw " .com.texh.log.custom.exemptions:" (rexfield extracting com.texh.log.custom.exemptions:)
| rex field=foo "(?regex for extracting a word before :)"
| stats count by bar
Thanks for response...