- Splunk Answers
- :
- Splunk Administration
- :
- Getting Data In
- :
- Re: In Windows Security logs, why does Splunk inco...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Good morning,
I noticed that Splunk (v. 6.5.1) does not properly report some fields of security event logs collected.
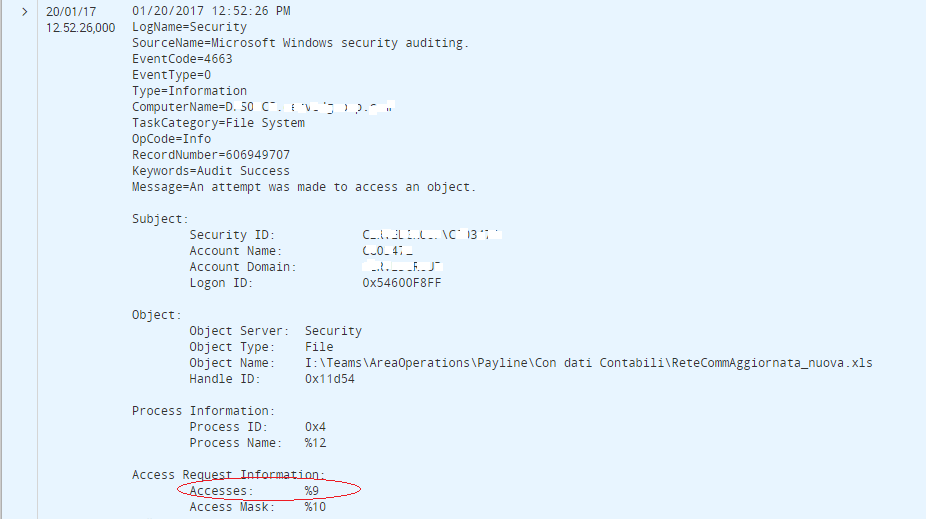
In the example, the value in the field "Accesses" of my Windows security log is : “ReadData (or ListDirectory)” but in the result of search in splunk I have : "%9"
And, unfortunately, also other fields are affected by the same problem!
Can someone help me?!
Thank you!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi patriziadepaola,
you should verify in Windows EventViewer if you have the same values.
I think that you should find the problem in Windows Event Logging, because Splunk acquires Windows Logs without modifying them.
Bye.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You need 2 things: you need AD (Domain Controller) setup correctly and you need this setting in your inputs.conf:
evt_resolve_ad_obj = 1
Read here (and elsewhere) for more:
https://answers.splunk.com/answers/23502/windows-sid-resolving-in-splunk.html
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi patriziadepaola,
you should verify in Windows EventViewer if you have the same values.
I think that you should find the problem in Windows Event Logging, because Splunk acquires Windows Logs without modifying them.
Bye.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Giuseppe, no I don't use soucetype=WinEventLog:Security
this is my inputs.conf:
[WinEventLog://ForwardedEvents]
disabled = 1
start_from = oldest
current_only = 0
evt_resolve_ad_obj = 1
checkpointInterval = 5
index = security
_TCP_ROUTING= collaudo
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Giuseppe, using TA_Windows Security Stanza with soucetype WinEventLog:Security all woks fine!
Thank you.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
If this answer solves your question, please accept it.
bye.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi Patrizia,
if you don't want to use this sourcetype, you have to rebuild all the WinEventLog:Security environment in your sourcetype.
See in Splunk_TA-Windows props.conf file what are all the configurations for WinEventLog:Security (you can find in "###### Windows Security Event Log ######" section) and rebuild them for your sourcetype.
Bye.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi patrizia,
how you took logs, using TA_Windows Security Stanza?
[WinEventLog://Security]
disabled = 1
start_from = oldest
current_only = 0
evt_resolve_ad_obj = 1
checkpointInterval = 5
and sourcetype=WinEventLog:Security?
Bye.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi patrizia,
You should try to use this sourcetype, because Splunk gives by default all the Windows configurations to ingest this logs.
Otherwise, you should search in Splunk_TA-Windows props.conf file extracting all the configurations for WinEventLog:Security (you can find in "###### Windows Security Event Log ######" section).
But Every Way I suggest to you to use the default sourcetype, it's easier!
Bye.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
No, unfortunately, in the windows log contain the correct messages! In the example that I had submitted, windows security log for string Accesses presents the value "ReadData (or ListDirectory)", but my search in splunk returns %9