Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Getting Data In
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- Splunk Answers
- :
- Splunk Administration
- :
- Getting Data In
- :
- Why does INGEST_EVAL duplicate my events if I assi...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
peter_krammer
Communicator
08-05-2021
06:58 AM
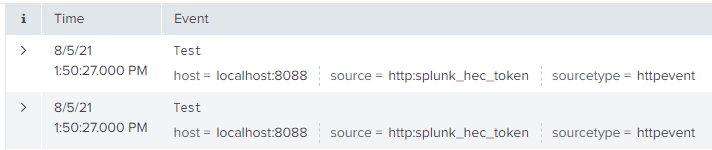
When I configure INGEST_EVAL to replace _raw with something else, it duplicates the event.
Splunk Enterprise Version 8.2.1
props.conf:
Spoiler
[source::http:splunk_hec_token]
TRUNCATE = 500000
SHOULD_LINEMERGE = false
KV_MODE = json
TRANSFORMS-fdz_event = fdz_event
TRUNCATE = 500000
SHOULD_LINEMERGE = false
KV_MODE = json
TRANSFORMS-fdz_event = fdz_event
transforms.conf
Spoiler
[fdz_event]
INGEST_EVAL = _raw="Test"
INGEST_EVAL = _raw="Test"
Output:
1 Solution
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
peter_krammer
Communicator
08-05-2021
07:50 AM
I found a workaround to circumvent this bug.
tranforms.conf
Spoiler
[fdz_event]
INGEST_EVAL = _raw="Test", queue=if(isnull(timestamp),"nullQueue", queue)
INGEST_EVAL = _raw="Test", queue=if(isnull(timestamp),"nullQueue", queue)
Because I notices that one of the duplicates has an indexed field "timestamp::none" and the other does not. With this I am routing only one of the to the nullQueue and keep the other.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
peter_krammer
Communicator
08-05-2021
07:50 AM
I found a workaround to circumvent this bug.
tranforms.conf
Spoiler
[fdz_event]
INGEST_EVAL = _raw="Test", queue=if(isnull(timestamp),"nullQueue", queue)
INGEST_EVAL = _raw="Test", queue=if(isnull(timestamp),"nullQueue", queue)
Because I notices that one of the duplicates has an indexed field "timestamp::none" and the other does not. With this I am routing only one of the to the nullQueue and keep the other.
Get Updates on the Splunk Community!
Stay Connected: Your Guide to May Tech Talks, Office Hours, and Webinars!
Take a look below to explore our upcoming Community Office Hours, Tech Talks, and Webinars this month. This ...
They're back! Join the SplunkTrust and MVP at .conf24
With our highly anticipated annual conference, .conf, comes the fez-wearers you can trust! The SplunkTrust, as ...
Enterprise Security Content Update (ESCU) | New Releases
Last month, the Splunk Threat Research Team had two releases of new security content via the Enterprise ...
