Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Splunk Search
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: Separate the fields from a merged result
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Separate the fields from a merged result
s_kandula
Observer
04-21-2020
01:03 PM
Hi
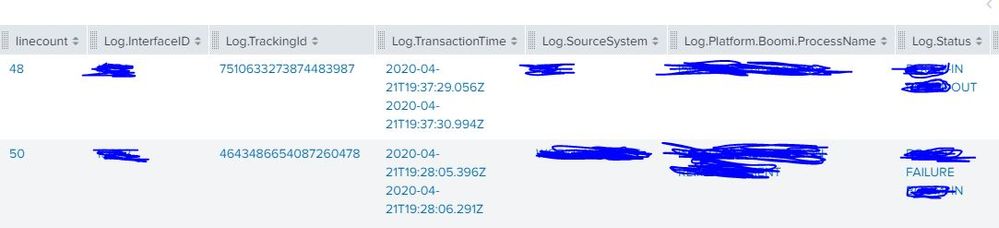
I have two events with following fields
Event 1
Log.Status : IN
TransactionTime : IN time
Tracking id: Unique ID (common between Event 1 and 2)
Event 2
Log.Status :OUT
TransactionTime: OUTtime
Trackingid
I merged the events using tracking ID and i got the required fields. But under transactionTime, I am seeing two times (IN and OUT) one below the other. Is there a way to list the times as separate fields in the merge results.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
to4kawa
Ultra Champion
04-21-2020
02:11 PM
use mvindex in eval
https://docs.splunk.com/Documentation/Splunk/latest/SearchReference/Eval
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
s_kandula
Observer
04-21-2020
02:19 PM
Thanks , I was able to get two separate fields based on the Status using the eval command.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
to4kawa
Ultra Champion
04-21-2020
02:47 PM
I see, please accept my answer.
Get Updates on the Splunk Community!
Stay Connected: Your Guide to May Tech Talks, Office Hours, and Webinars!
Take a look below to explore our upcoming Community Office Hours, Tech Talks, and Webinars this month. This ...
They're back! Join the SplunkTrust and MVP at .conf24
With our highly anticipated annual conference, .conf, comes the fez-wearers you can trust! The SplunkTrust, as ...
Enterprise Security Content Update (ESCU) | New Releases
Last month, the Splunk Threat Research Team had two releases of new security content via the Enterprise ...