- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: Group events by specific field and generate ti...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
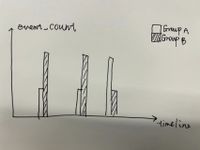
Grouping events by specific field and generate timechart for both groups?
There is a complicated requirement for me, the splunk beginner. Hope you can give me some advice.
The splunk version: 9.0.2303.201
Since there are a lot of logs(events) that meet my search requirement, I want to generate a time chart with those logs.
I want to group those logs by a specific field named "field1":
For events in group A, their "field1" value is unique when compared with all other events;
For events in group B, their "field1" value has been repeated once when compared with other events, which means when I search the value of "field1"(group B), it will return two events.
Based on this premise, I want to count the event that happened times of both two groups, and display them in a timeline(time chart), what can I do?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You can use the grouping you explained with some splunk commands to accomplish that.
| windbag
| eval group = if(lang="Euro","groupA","groupB")
| timechart count by groupThis is just an example with random data that you can try in your environment . You can change your grouping conditions in the if statement to your field1=your unique value.
Hope I was able to help you. If so, some karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello @Sanshan Would you be able to share example with values? Also, an image with the expected chart would be helpful to answer
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sure, the "field1" has a value of random UUID to mark a single trigger behavior.
But in some cases, it returns two times' logs with the same UUID, so I really need to separate the two situations(A: A unique UUID only appeared in one event; B: In two different events, they have the same UUID).
For the chart: