Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Security
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- Splunk Answers
- :
- Splunk Administration
- :
- Security
- :
- How do i re-ingest data from a particular source?
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How do i re-ingest data from a particular source?
sathiyasun
Explorer
11-15-2023
08:51 AM
I had a missing data from a certain date and time range. How would i re-ingest the data into splunk from a UF.
Below is the inputs.conf
[monitor:///app/java/servers/app/log/app.log.2023-11-12]
index = app_logs
ignoreOlderThan = 10d
disabled = false
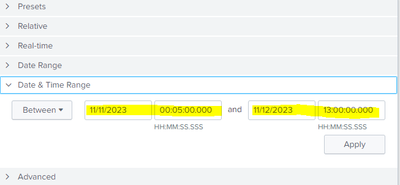
sourcetype = javalogsIts missing data from Nov-11 00:05 till Nov-12 13:00 so how would i just reinject the data only for that certain data/time period.
It just one log file for a day although we have some events so how would i regest only the missing data for the time period and please let me know the config.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
richgalloway

SplunkTrust
11-15-2023
04:35 PM
A common way to re-ingest data is by using the splunk add oneshot command. Splunk will re-ingest everything in the file, however, without regard to events that were previously indexed. To ingest only missing events, I would copy the file and remove the events that you don't want to read in again.
---
If this reply helps you, Karma would be appreciated.
If this reply helps you, Karma would be appreciated.
Get Updates on the Splunk Community!
Stay Connected: Your Guide to May Tech Talks, Office Hours, and Webinars!
Take a look below to explore our upcoming Community Office Hours, Tech Talks, and Webinars this month. This ...
They're back! Join the SplunkTrust and MVP at .conf24
With our highly anticipated annual conference, .conf, comes the fez-wearers you can trust! The SplunkTrust, as ...
Enterprise Security Content Update (ESCU) | New Releases
Last month, the Splunk Threat Research Team had two releases of new security content via the Enterprise ...