Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
All Apps and Add-ons
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- Apps and Add-ons
- :
- All Apps and Add-ons
- :
- Re: RegEx Help
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
RegEx Help
jerinvarghese
Communicator
04-22-2020
10:18 PM
Need help in RegEx output.
Below is my _raw input
"<MTIER><TID: 0000000181> <CATEGORY:com.remedy.log.WEBSERVICES > /* Wed Apr 22 2020 14:49:21.277 */ <LEVEL: FINE > <Class: com.remedy.arsys.ws.services.ARService><Method: performOperation><TENANT: null > <USER: na\xsmoogitsm > input document: <?xml version=""1.0"" encoding=""UTF-8""?>
<ROOT><Incident_Number>INC000013542725</Incident_Number><Work_Log_Type>General Information</Work_Log_Type><Locked>No</Locked><View_Access>Public</View_Access><Summary>AlertID: 171945364 : Open : USWNK-WANRTC001 : Node is down.
Class:Custom Trap
Host: uswnk-wanrtc001.</Summary><Notes>AlertID: 171945364 : Open : USWNK-WANRTC001 : Node is down.
Class:Custom Trap
Host: uswnk-wanrtc001.sa.xom.com
External ID: 34217579
Tier: 3
Impact: 2-Significant/Large
Urgency: 2-High</Notes><z2AF_Attachment1_attachmentOrigSize>0</z2AF_Attachment1_attachmentOrigSize><z2AF_Attachment2_attachmentOrigSize>0</z2AF_Attachment2_attachmentOrigSize><z2AF_Attachment3_attachmentOrigSize>0</z2AF_Attachment3_attachmentOrigSize></ROOT>"
I want below content to be filtered.
Class:Custom Trap
Open : USWNK-WANRTC001 : Node is down.
Host: uswnk-wanrtc001.sa.xom.com
Impact: 2-Significant/Large
Urgency: 2-High
INC000013542725
AlertID: 171945364
Wed Apr 22 2020 14:49:21.277
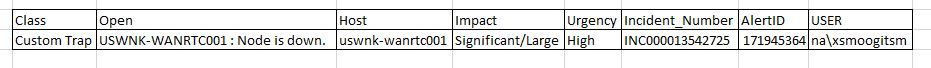
expected table output.
In tabular
There are spaces and punctuations were am facing challenges.
Please help me with this.
Few of the field I tried to capture.
| rex field=_raw "Incident_Number\W(?<ITSM_Number>.*)\W\WIncident_Number\W.*"
| rex field=_raw "(Host:\s)(?<Hostname>[^\.<]+\.)"
| rex field=_raw "(Urgency:\s)(?<Urgency>\S-\D*[{lmwh}$])"
| rex field=_raw "(AlertID:\s)(?<AlertID>[^\D*]+)"
| rex field=_raw "(Open\s:\s)(?<Description>[^\.*]+)"
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
jawahir007
Path Finder
04-22-2020
11:48 PM
Try this: -
|rex "Class:(?<Class>[^:\n]*)\s*Host:.*\s*External\s*ID"|rex "Open\s*:\s*(?<Open>.*)\n"|rex "Host:(?<Host>.*)\s*External\s*ID"|rex "Impact:\s*\d*\-?(?<Impact>.*)\n"|rex "Urgency:\s*\d*\-?(?<Urgency>.*)<\/Notes"|rex "Incident_Number>\s*(?<Incident_Number>.*)<\/Incident_Number"|rex "Summary>AlertID:\s*(?<AlertID>\d*)"|rex "USER:\s*(?<USER>[^\s>]*)"|table Class,Open,Host,Impact,Urgency,Incident_Number,AlertID,USER
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
manjunathmeti
Champion
04-22-2020
11:43 PM
hi @jerinvarghese,
Try this:
| rex "(?<root>\<ROOT\>[\w\W\s]+\<\/ROOT\>)"
| spath input=root
| rex field=ROOT.Notes "AlertID[:\s]*(?<AlertID>\d+)[:\s]*(?<Description>[\w\W\s]+)\s*Class[:\s]*(?<Class>[\w\s]+)\s*Host[:\s]*(?<Host>[\w\W\.]+)\s*External\sID[:\s]*(?<External_ID>\d+)\s*Tier[:\s]*(?<Tier>\d+)\s*Impact[:\s]*(?<Impact>[\w\W]+)\s*Urgency[:\s]*(?<Urgency>[\w\-]+)"
| rex "\/\*\s(?<dateTime>[\w\s:\.]+)\s\*\/"
| rex "\<USER:\s(?<USER>[^\>]+)\>"
| table AlertID, Description, Class,Host, External_ID, Tier, Impact, Urgency, dateTime, USER
Without spath:
| rex "AlertID[:\s]*(?<AlertID>\d+)[:\s]*(?<Description>[\w\s:\-\.]+)\s*Class[:\s]*(?<Class>[\w\s]+)\s*Host[:\s]*(?<Host>[\w\-\.]+)\s*External\sID[:\s]*(?<External_ID>\d+)\s*Tier[:\s]*(?<Tier>\d+)\s*Impact[:\s]*(?<Impact>[\w\W]+)\s*Urgency[:\s]*(?<Urgency>[\w\-]+)"
| rex "\/\*\s(?<dateTime>[\w\s:\.]+)\s\*\/"
| rex "\<USER:\s(?<USER>[^\>]+)\>"
| table AlertID, Description, Class,Host, External_ID, Tier, Impact, Urgency, dateTime, USER
Sample query:
| makeresults
| eval _raw= "<MTIER><TID: 0000000181> <CATEGORY:com.remedy.log.WEBSERVICES> /* Wed Apr 22 2020 14:49:21.277 */ <LEVEL: FINE > <Class: com.remedy.arsys.ws.services.ARService><Method: performOperation><TENANT: null> <USER: na\xsmoogitsm> input document: <?xml version=\"1.0\" encoding=\"UTF-8\"?>
<ROOT><Incident_Number>INC000013542725</Incident_Number><Work_Log_Type>General Information</Work_Log_Type><Locked>No</Locked><View_Access>Public</View_Access><Summary>AlertID: 171945364 : Open : USWNK-WANRTC001 : Node is down.
Class:Custom Trap
Host: uswnk-wanrtc001.</Summary><Notes>AlertID: 171945364 : Open : USWNK-WANRTC001 : Node is down.
Class:Custom Trap
Host: uswnk-wanrtc001.sa.xom.com
External ID: 34217579
Tier: 3
Impact: 2-Significant/Large
Urgency: 2-High</Notes><z2AF_Attachment1_attachmentOrigSize>0</z2AF_Attachment1_attachmentOrigSize><z2AF_Attachment2_attachmentOrigSize>0</z2AF_Attachment2_attachmentOrigSize><z2AF_Attachment3_attachmentOrigSize>0</z2AF_Attachment3_attachmentOrigSize></ROOT>"
| rex "(?<root>\<ROOT\>[\w\W\s]+\<\/ROOT\>)"
| spath input=root
| rex field=ROOT.Notes "AlertID[:\s]*(?<AlertID>\d+)[:\s]*(?<Description>[\w\W\s]+)\s*Class[:\s]*(?<Class>[\w\s]+)\s*Host[:\s]*(?<Host>[\w\W\.]+)\s*External\sID[:\s]*(?<External_ID>\d+)\s*Tier[:\s]*(?<Tier>\d+)\s*Impact[:\s]*(?<Impact>[\w\W]+)\s*Urgency[:\s]*(?<Urgency>[\w\-]+)"
| rex "\/\*\s(?<dateTime>[\w\s:\.]+)\s\*\/"
| rex "\<USER:\s(?<USER>[^\>]+)\>"
| table AlertID, Description, Class,Host, External_ID, Tier, Impact, Urgency, dateTime, USER
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
jerinvarghese
Communicator
04-23-2020
02:14 AM
Please help in adding Incident_Number also to the search
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
manjunathmeti
Champion
04-23-2020
02:22 AM
Try this:
| rex "AlertID[:\s]*(?<AlertID>\d+)[:\s]*(?<Description>[\w\s:\-\.]+)\s*Class[:\s]*(?<Class>[\w\s]+)\s*Host[:\s]*(?<Host>[\w\-\.]+)\s*External\sID[:\s]*(?<External_ID>\d+)\s*Tier[:\s]*(?<Tier>\d+)\s*Impact[:\s]*(?<Impact>[\w\W]+)\s*Urgency[:\s]*(?<Urgency>[\w\-]+)"
| rex "\/\*\s(?<dateTime>[\w\s:\.]+)\s\*\/"
| rex "\<USER:\s(?<USER>[^\>]+)\>"
| rex "\<Incident_Number\>(?<Incident_Number>[^\>]+)\<\/Incident_Number\>"
| table AlertID, Description, Class,Host, External_ID, Tier, Impact, Urgency, dateTime, USER, Incident_Number
Get Updates on the Splunk Community!
Stay Connected: Your Guide to May Tech Talks, Office Hours, and Webinars!
Take a look below to explore our upcoming Community Office Hours, Tech Talks, and Webinars this month. This ...
They're back! Join the SplunkTrust and MVP at .conf24
With our highly anticipated annual conference, .conf, comes the fez-wearers you can trust! The SplunkTrust, as ...
Enterprise Security Content Update (ESCU) | New Releases
Last month, the Splunk Threat Research Team had two releases of new security content via the Enterprise ...