- Splunk Answers
- :
- Splunk Administration
- :
- Getting Data In
- :
- Why is Windows host not populated corretly for WEF...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Why is Windows host not populated corretly for WEF server ni workgroup
Hello,
I have a WEC server which already collects logs from domain servers (http) and workgroup servers (https).
As I am testing splunk as a SIEM I have installed a forwarder on that host which forward the "Forwarded Events" log.
To map the ComputerName to the host in splunk I have added the following in inputs.conf at the forwarder level : host = WinEventLogForwardHost
So far so good except for the workgroup host logs where the ComputerName is a obviously simple hostname instead of a fqdn.
In this case, splunk put almost the full log in host until it finds a ".".
So I guess that there is a process somewhere which parse the fqdn (until the first ".") to add only the server name in host.
Moreover, this creates a lot of hosts in data summary.
Is there a way to make splunk understand the Windows logs correctly? This should be out-of-the-box 🙂
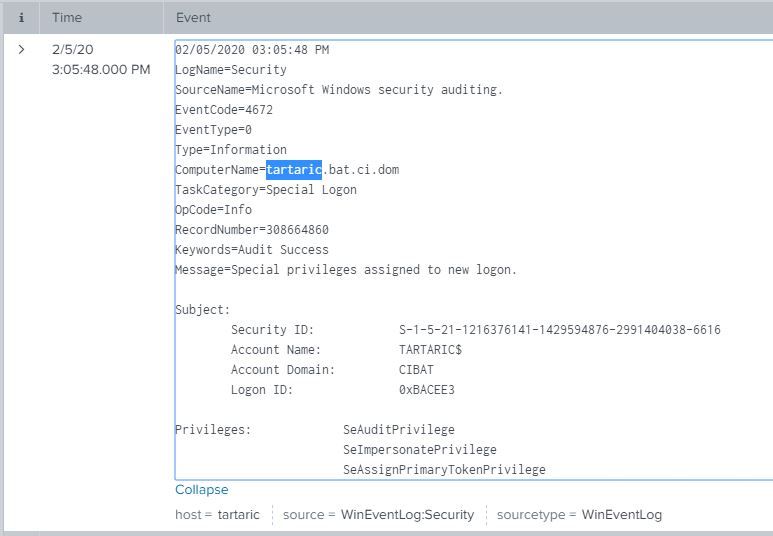
This one is correct
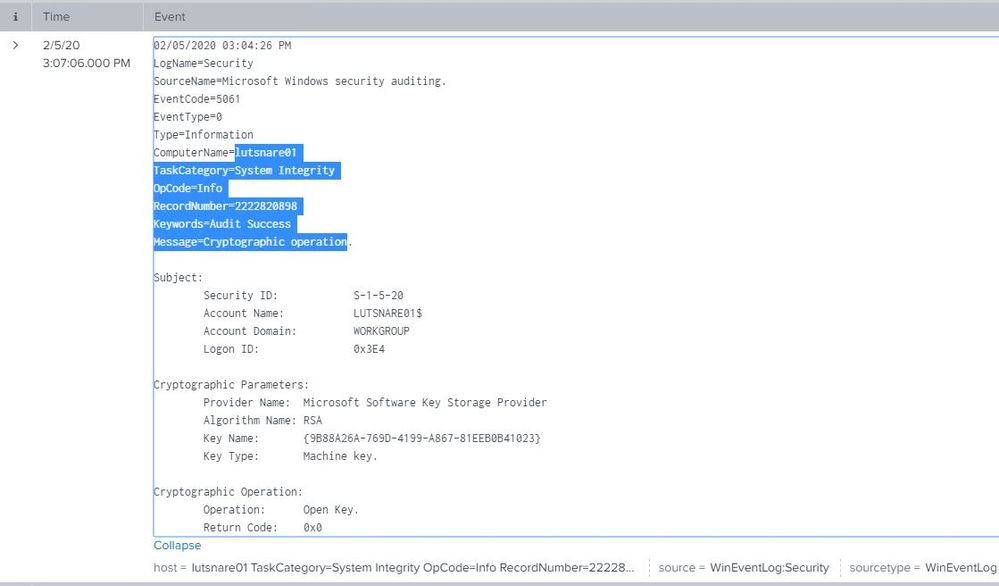
This one is not correct and take the log until the first "." as host
Thanks
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Check out the Splunk Add-on for Microsoft Windows at https://splunkbase.splunk.com/app/742/.
If this reply helps you, Karma would be appreciated.