Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Splunk Enterprise Security
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- Splunk Answers
- :
- Splunk Premium Solutions
- :
- Security Premium Solutions
- :
- Splunk Enterprise Security
- :
- Active Directory - Event ID 4738 - Message Fields
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Active Directory - Event ID 4738 - Message Fields
fzuazo
Path Finder
08-28-2018
11:59 AM
I seem to be having some issues working with AD event ID 4738. Unless I am doing or reading something wrong, one of the attributes clearly has a value in raw AD log yet Splunk does not seem to capture that value.
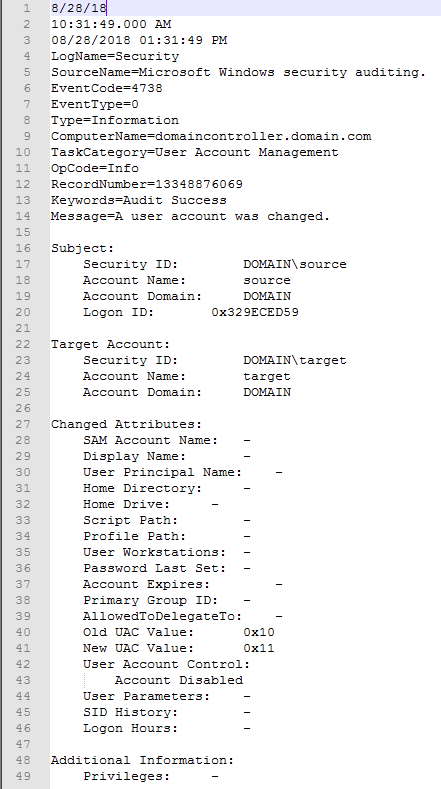
Below is a screenshot of an event 4738. See the "User Account Control" field and how it shows "Account Disabled". Under this screenshot I have included another showing how Splunk displays the returned values for that attribute. I have attempted to use REX but seeing as Splunk doesn't see the value for "User Account Control" it isn't returning anything.
My goal is to be able to create a table showing the source, target, the change, and time. I can populate the other columns just fine.
Any help is GREATLY appreciated.
Get Updates on the Splunk Community!
Extending Observability Content to Splunk Cloud
Watch Now!
In this Extending Observability Content to Splunk Cloud Tech Talk, you'll see how to leverage ...
More Control Over Your Monitoring Costs with Archived Metrics!
What if there was a way you could keep all the metrics data you need while saving on storage costs?This is now ...
New in Observability Cloud - Explicit Bucket Histograms
Splunk introduces native support for histograms as a metric data type within Observability Cloud with Explicit ...