- Apps and Add-ons
- :
- All Apps and Add-ons
- :
- Why am I not getting any data on Palo Alto Network...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
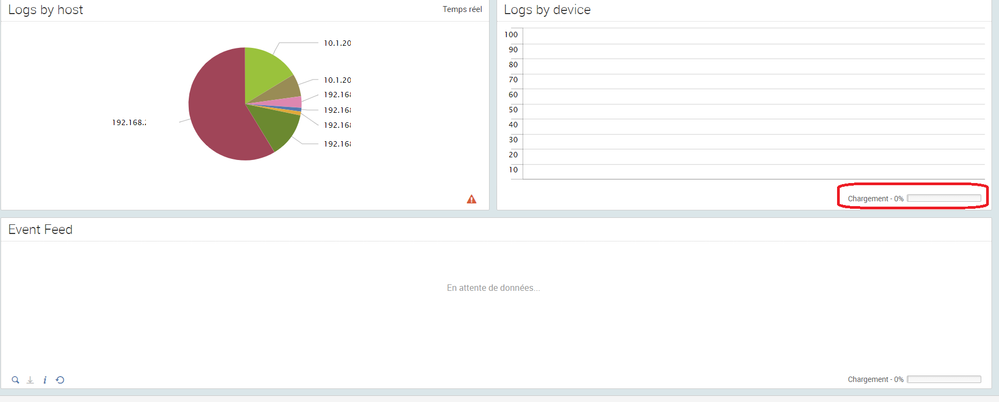
Why am I not getting any data on Palo Alto Networks App for Splunk?
Hello
Splunk Version 6.2.1
Palo Alto Networks APP 6.0.1
The index seems to be correctly configured because I receive data if I search "eventtype=pan" or "index="pan_logs" on the App itself.
But I have no data at all under Activity, Threats or Operations tab...
I followed the troubleshooting steps available but found nothing, only something about NTP and time settings, but that's not clear that the NTP problem makes the data not to appear at all.
And the timestamp of logs seems correct:
What else can I check? This is my first configs on Splunk and I may have missed something.
Thanks for the help!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The add-on is required for parsing. Does the operations > real time events dashboard work?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Are some dashboards working or non at all? What version of the Add-on do you have installed?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes, I have some working dashboards, but only for others App, like network ones.
The Add one is 6.0.2, but I think I don't need this Add On, I have configured nothing on it.
Thanks !
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Can you retrieve the search query for one of the non functioning dashboards and paste it here please?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Firewall Event, Latest event code is this one:
| pan_tstats count FROM node(log.system) $serial_number$ $vsys$ $description$ $log_subtype$ $severity$ $event_id$ table(_time log.serial_number log.description log.log_subtype log.severity log.event_id) | sort -_time
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
And what's displayed is "waiting for entries"