Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Splunk Search
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Doing calculations using eval command with fields ...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
jvmerilla
Path Finder
11-29-2017
09:41 PM
Hi,
I'm doing some search query where I used timechart command that creates fields. Now, what I want to do is to some calculations with this fields using eval command but nothing happens.
Here's my query:
index="sample_data" sourcetype="management_sampledata.csv"
| timechart count(Ticket_No) as Inflow
| append
[search index="sample_data" sourcetype="management_sampledata.csv" Status=Closed
| timechart count(Ticket_No) as Closed/Cancelled
| fillnull]
| timechart first(*) as *
| eval Backlog_Total = (Inflow-Closed/Cancelled)
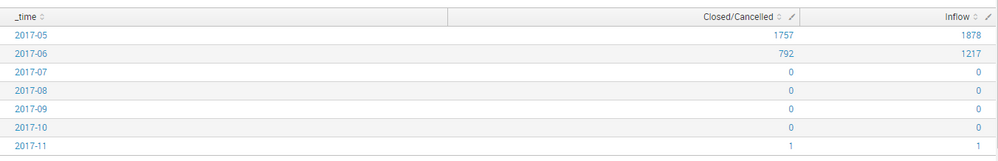
And here's the result:
What I was expecting to happen is a new field named "Backlog_Total" will be created using the eval command.
I hope someone can help me with this.
Thank you.
1 Solution
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
kamlesh_vaghela

SplunkTrust
11-29-2017
11:33 PM
Hi
Can you please try this?
index="sample_data" sourcetype="management_sampledata.csv"
| timechart count(Ticket_No) as Inflow
| append
[search index="sample_data" sourcetype="management_sampledata.csv" Status=Closed
| timechart count(Ticket_No) as "Closed/Cancelled"
| fillnull]
| timechart first(*) as *
| eval Backlog_Total = (Inflow-'Closed/Cancelled')
I have just changed in Closed/Cancelled field.
Thanks
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
kamlesh_vaghela

SplunkTrust
11-29-2017
11:33 PM
Hi
Can you please try this?
index="sample_data" sourcetype="management_sampledata.csv"
| timechart count(Ticket_No) as Inflow
| append
[search index="sample_data" sourcetype="management_sampledata.csv" Status=Closed
| timechart count(Ticket_No) as "Closed/Cancelled"
| fillnull]
| timechart first(*) as *
| eval Backlog_Total = (Inflow-'Closed/Cancelled')
I have just changed in Closed/Cancelled field.
Thanks
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
jvmerilla
Path Finder
11-29-2017
11:55 PM
Hi @kamlesh_vaghela,
It works!
Thank you again. 🙂
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
kamlesh_vaghela

SplunkTrust
11-30-2017
12:07 AM
Glad to help you.
Can you please accept the answer to close this question and upvote any comment which helps you.
Happy Splunking
Get Updates on the Splunk Community!
Get Your Exclusive Splunk Certified Cybersecurity Defense Engineer at Splunk .conf24 ...
We’re excited to announce a new Splunk certification exam being released at .conf24! If you’re headed to Vegas ...
Share Your Ideas & Meet the Lantern team at .Conf! Plus All of This Month’s New ...
Splunk Lantern is Splunk’s customer success center that provides advice from Splunk experts on valuable data ...
Combine Multiline Logs into a Single Event with SOCK: a Step-by-Step Guide for ...
Combine multiline logs into a single event with SOCK - a step-by-step guide for newbies
Olga Malita
The ...