- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Can I combine two searches and group by _time usin...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Can I combine two searches and group by _time using a regex filter?
Hello,
I'm relatively new to Splunk, so please bear with me. What I am trying to accomplish is a time chart using tstats, but filtering the results using a regex. Specifically, this is for counting the number of times someone connects over HTTP/S to a naked IP (IP specified instead of a URL). The following two queries work, but when I try to combine them I get zero results:
| tstats count(Web.dest) AS destCount FROM datamodel=Web WHERE Web.action=blocked GROUPBY Web.dest | regex Web.dest="\d{1,3}\.\d{1,3}\.\d{1,3}\.\d{1,3}$"
As you can see in the below screenshot, when grouped by Web.dest I get a table with counts and the regex filter works fine.
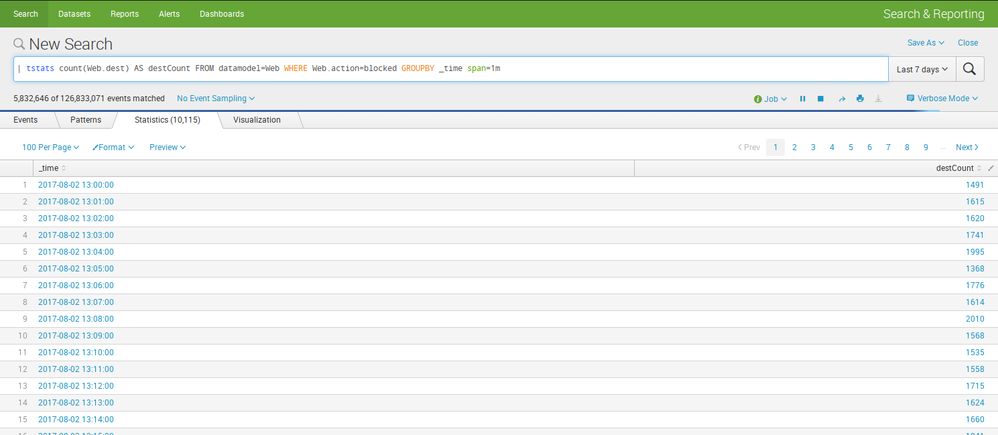
| tstats count(Web.dest) AS destCount FROM datamodel=Web WHERE Web.action=blocked GROUPBY _time span=1m
As you can see in the below screenshot, when grouped by _time without the regex, I get a nice table which I can then use to create a time chart.
However, if I try to combine the two queries and group by _time using a regex filter, I get zero results (screenshot not needed I think).
| tstats count(Web.dest) AS destCount FROM datamodel=Web WHERE Web.action=blocked GROUPBY _time span=1m | regex Web.dest="\d{1,3}\.\d{1,3}\.\d{1,3}\.\d{1,3}$"
Can anyone assist me and/or confirm if what I'm trying to do is even possible? Your assistance is greatly appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The query your tried is just grouping by _time to no Web.dest field is available to filter. Try like this
| tstats count(Web.dest) AS destCount FROM datamodel=Web WHERE Web.action=blocked GROUPBY Web.dest _time span=1m | regex Web.dest="\d{1,3}\.\d{1,3}\.\d{1,3}\.\d{1,3}$"