Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Splunk Search
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- How to edit my search to send an email if the coun...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How to edit my search to send an email if the count of a down server is greater than 0?
jampar12
New Member
06-26-2017
01:31 PM
I'm new to Splunk and I have the Search where I check one Server for 7 Services and State=Stopped and run a stats count at the end and I'd to send out a email if the count > 0
index="*windows" host=Q9BVPAVACT01 sourcetype=WinHostMon source=service Name=CyberTechDatabase* OR (index="*windows" host=Q9BVPAVACT01 sourcetype=WinHostMon source=service Name="CybertechmediaManager" ) OR (index="*windows" host=Q9BVPAVACT01 sourcetype=WinHostMon source=service Name=CybertechlicenseService ) OR (index="*windows" host=Q9BVPAVACT01 sourcetype=WinHostMon source=service Name="CyberTechSystemManager" ) OR (index="*windows" host=Q9BVPAVACT01 sourcetype=WinHostMon source=service Name="CybertechUserManager" ) OR (index="*windows" host=Q9BVPAVACT01 sourcetype=WinHostMon source=service Name="MySQL" ) OR (index="*windows" host=Q9BVPAVACT01 sourcetype=WinHostMon source=service Name="CybertechRecord*" ) State=Stopped | stats count
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
mbuehler_splunk

Splunk Employee
06-26-2017
02:39 PM
aaraneta,
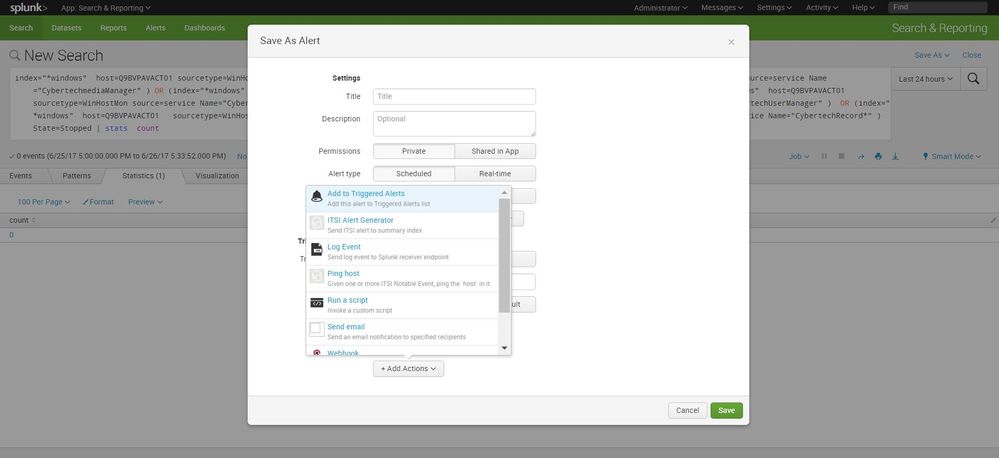
So the first thing you want to do is click save as:
![alt text][1]
Then after you click this, select Alert:
[1]: /storage/temp/207661-cap1.jpgThen You will want to select the time window that you want the search to run in and the frequency, then select the add action from the triggered actions section, selecting send email:
If you have not setup your email server here is a guide to doing that.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
jkat54

SplunkTrust
06-26-2017
02:52 PM
You can greatly simplify this search too:
ex:
index=*windows host=Q9BVPAVACT01 State=Stopped source=service| stats count by Name | where count > 0
Get Updates on the Splunk Community!
.conf24 | Registration Open!
Hello, hello! I come bearing good news: Registration for .conf24 is now open!
conf is Splunk’s rad annual ...
ICYMI - Check out the latest releases of Splunk Edge Processor
Splunk is pleased to announce the latest enhancements to Splunk Edge Processor.
HEC Receiver authorization ...
Introducing the 2024 SplunkTrust!
Hello, Splunk Community! We are beyond thrilled to announce our newest group of SplunkTrust members!
The ...