- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- How to write regex for filtering values with .,: i...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How to write regex for filtering values with .,: in same field
Hi,
I have below values in same field , i have to take the values(characters) before : .If the first value is ip address then full ip have to taken.
for example ,
10.102.208.108:sqlexpress( need full ip address from here)
ALATDEV1:OMGEO(Need ALATDEV1 from here)
SWSYBQ21.dtcc.com:1025 (Need SWSYBQ21 from here )
SWTEPQ0004.corp.dtcc.com:172.21.168.62:172.21.168.62:0:ServiceList.WebInspect Data Server (Need SWTEPQ0004)
Please suggest me .
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This should work for all the cases if say the values are in field called testField:
your query to return testField
| rex field=testField "^(?<myField>(([\d\.]+)|(\w+)))[:.]"
| table myField
See extraction here.
You can also replace the last capturing group [:.] to include comma if required [:.,]
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
hi gokandroid,
Thank you and this works perfectly ..
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Will it be possible for you to give complete event as example i.e. whether there is a pattern before and pattern after the field you are trying to extract?
If not can you try Interactive Field Extraction to let Splunk generate regular expression for the required field extraction. In your test machine you can add some sample logs and use Extract New Fields option.
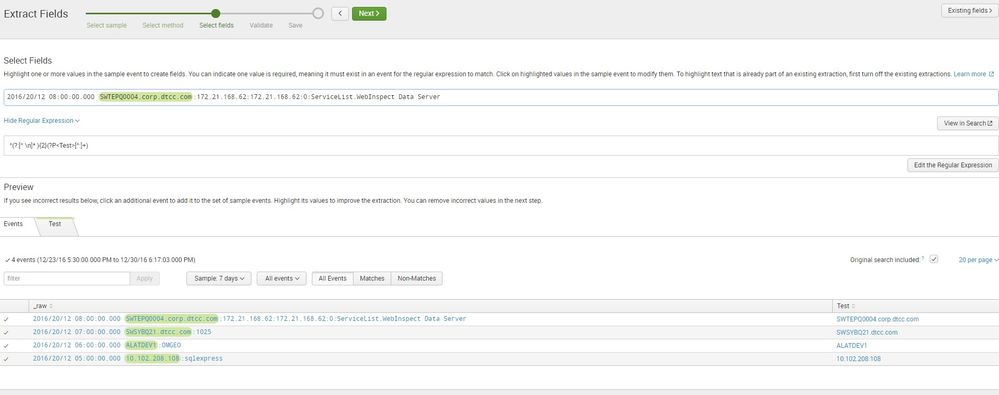
Refer to attached screenshot for a sample regular expression based IFX.
| makeresults | eval message= "Happy Splunking!!!"
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi umsundar2015,
Try something like this
^(?<field>[^:]*)
Bye.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
Thank you for your rex.
But still for this CVSQLP0001.corp.reds.com:MSSQLSERVER , i am getting CVSQLP0001.corp.reds.com
My requirement is to get CVSQLP0001 for the above scenario too.
Pls advice me .
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
try this
^(?<field>[^:.]*)
Bye.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
now the ip address is not proper , iam getting 10 alone for 10.102.208.108:SQLEXPRESS,
Pls suggest
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
try this
^(?<field>((\d+\.\d+\.\d+\.\d+)|(\w+))*)
Bye.
Giuseppe
