Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Alerting
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- Splunk Answers
- :
- Using Splunk
- :
- Alerting
- :
- How to create a single alert to trigger only when ...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How to create a single alert to trigger only when a threshold is passed by a single index, not all indexes combined?
khagan
Path Finder
09-18-2015
07:57 AM
Hi everyone,
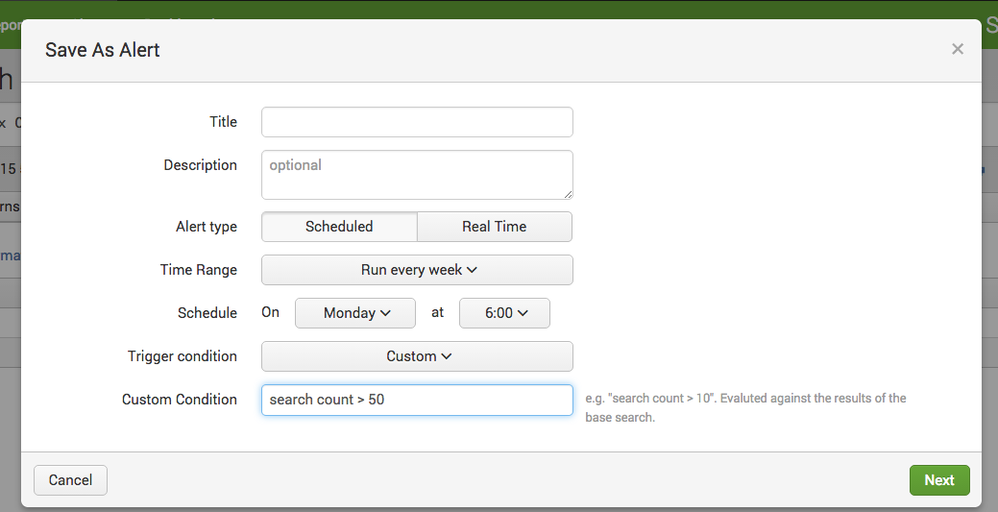
I'm trying to write an alert, covering all indexes, that triggers when a specific number (say, 50) of events occur. However, I only want the alert to trigger if all 50 events are in the same index, not, for example, 40 in one index and 10 in another. Is there a way to specify this in the search string, or would I need to have a different alert for each index?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
sover
Engager
09-24-2015
02:56 PM
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
somesoni2
Revered Legend
09-18-2015
11:19 AM
Will something like this would work
| tstats count WHERE index=* by index | where count>50
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Federica_92
Communicator
09-24-2015
03:09 AM
the problem is that this query return only the number of every index, if it's higher than 50, I need something like:
sourcetype=windows EventId=X status=Y earliest=-5m | stats count by EventID | where count>5 | search tstats count WHERE index=* by index| where count>0
Basically I need to execute the first part of the query, for all the indexes, but I need to display separate results for each of the indexes.
Is it possible?
Get Updates on the Splunk Community!
Introducing the 2024 SplunkTrust!
Hello, Splunk Community! We are beyond thrilled to announce our newest group of SplunkTrust members!
The ...
Introducing the 2024 Splunk MVPs!
We are excited to announce the 2024 cohort of the Splunk MVP program. Splunk MVPs are passionate members of ...
Splunk Custom Visualizations App End of Life
The Splunk Custom Visualizations apps End of Life for SimpleXML will reach end of support on Dec 21, 2024, ...