- Apps and Add-ons
- :
- All Apps and Add-ons
- :
- JMS Messaging Modular Input: How to call a data in...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We have installed the 'JMS Messaging Modular Input' application in Splunk 6.1. It works fine if the 'JNDI Provider URL' is non SSL such as:
tcp://localhost:61617
When we change our broker to use SSL i.e. ssl://localhost:61617, Splunk throws an exception, since it cannot find the broker's certificate
This is the exception:
message from "python C:\Splunk\etc\apps\jms_ta\bin\jms.py" Caused by: javax.net.ssl.SSLHandshakeException: sun.security.validator.ValidatorException: PKIX path building failed: sun.security.provider.certpath.SunCertPathBuilderException: unable to find valid certification path to requested target
message from "python C:\Splunk\etc\apps\jms_ta\bin\jms.py" at sun.security.ssl.Alerts.getSSLException(Alerts.java:192)
message from "python C:\Splunk\etc\apps\jms_ta\bin\jms.py" at sun.security.ssl.SSLSocketImpl.fatal(SSLSocketImpl.java:1884)
message from "python C:\Splunk\etc\apps\jms_ta\bin\jms.py" at sun.security.ssl.Handshaker.fatalSE(Handshaker.java:276)
message from "python C:\Splunk\etc\apps\jms_ta\bin\jms.py" at sun.security.ssl.Handshaker.fatalSE(Handshaker.java:270)
message from "python C:\Splunk\etc\apps\jms_ta\bin\jms.py" at sun.security.ssl.ClientHandshaker.serverCertificate(ClientHandshaker.java:1341)
message from "python C:\Splunk\etc\apps\jms_ta\bin\jms.py" at sun.security.ssl.ClientHandshaker.processMessage(ClientHandshaker.java:153)
message from "python C:\Splunk\etc\apps\jms_ta\bin\jms.py" at sun.security.ssl.Handshaker.processLoop(Handshaker.java:868)
message from "python C:\Splunk\etc\apps\jms_ta\bin\jms.py" at sun.security.ssl.Handshaker.process_record(Handshaker.java:804)
message from "python C:\Splunk\etc\apps\jms_ta\bin\jms.py" at sun.security.ssl.SSLSocketImpl.readRecord(SSLSocketImpl.java:1016)
message from "python C:\Splunk\etc\apps\jms_ta\bin\jms.py" at sun.security.ssl.SSLSocketImpl.performInitialHandshake(SSLSocketImpl.java:1312)
message from "python C:\Splunk\etc\apps\jms_ta\bin\jms.py" at sun.security.ssl.SSLSocketImpl.writeRecord(SSLSocketImpl.java:702)
message from "python C:\Splunk\etc\apps\jms_ta\bin\jms.py" at sun.security.ssl.AppOutputStream.write(AppOutputStream.java:122)
I really can't find any documentation in Splunk that explains how to import the broker's certificate into Splunk's environment. All I see is the instructions on how to set up SSL between Splunk's nodes.
Has anyone been able work through this before or found a guide on how to set this up?
Thank you in advance.
-Juan
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I really can't find any documentation
in Splunk that explains how to import
the broker's certificate into Splunk's
environment. All I see is the
instructions on how to set up SSL
between Splunk's nodes.
This is nothing to do with core Splunk configuration. You are using the JMS Messaging Modular Input , so typically you would set JVM system properties for SSL client settings. Available properties are Googleable.
javax.net.ssl.keyStore
This property is used to specify the location of the key store. A key store is a database of key material that are used for various purposes, including authentication and data integrity. This property takes a String value. Any valid key store location can be assigned to this property. The default value is NULL.
javax.net.ssl.keyStoreType
This property denotes the type of the key store. It takes a String value. Any valid key store type supported by SSL can be assigned to this property. The default value is KeyStore.getDefaultValue().
javax.net.ssl.keyStorePassword
This property specifies the password of the key store. This password value is used to check the integrity of the data in the key store before accessing it. This property takes a String value. It does not have a default value.
javax.net.ssl.trustStore
This property is used to specify the location of the trust store. A trust store is a key store that is used when making decisions about which clients and servers can be trusted. The property takes a String value that specifies a valid trust store location. The default value is jssecacerts, if available, or cacerts.
javax.net.ssl.trustStoreType
This property denotes the type of the trust store. It takes a String value. Any valid trust store type supported by SSL can be assigned to this property. The default value is TrustStore.getDefaultValue().
javax.net.ssl.trustStorePassword
This property is used to set the password for the trust store. The trust store password is used to check the integrity of the data in the trust store before accessing it. The property takes a String value. It does not have any default value.
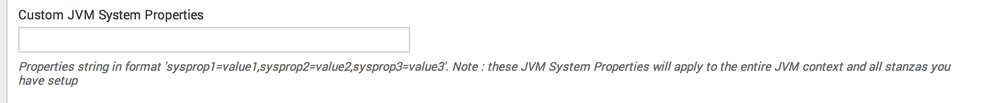
In the setup for your JMS stanza there is a field for entering these.
-Djavax.net.ssl.keyStore=somepath,-Djavax.net.ssl.keyStoreType=sometype, .......
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I really can't find any documentation
in Splunk that explains how to import
the broker's certificate into Splunk's
environment. All I see is the
instructions on how to set up SSL
between Splunk's nodes.
This is nothing to do with core Splunk configuration. You are using the JMS Messaging Modular Input , so typically you would set JVM system properties for SSL client settings. Available properties are Googleable.
javax.net.ssl.keyStore
This property is used to specify the location of the key store. A key store is a database of key material that are used for various purposes, including authentication and data integrity. This property takes a String value. Any valid key store location can be assigned to this property. The default value is NULL.
javax.net.ssl.keyStoreType
This property denotes the type of the key store. It takes a String value. Any valid key store type supported by SSL can be assigned to this property. The default value is KeyStore.getDefaultValue().
javax.net.ssl.keyStorePassword
This property specifies the password of the key store. This password value is used to check the integrity of the data in the key store before accessing it. This property takes a String value. It does not have a default value.
javax.net.ssl.trustStore
This property is used to specify the location of the trust store. A trust store is a key store that is used when making decisions about which clients and servers can be trusted. The property takes a String value that specifies a valid trust store location. The default value is jssecacerts, if available, or cacerts.
javax.net.ssl.trustStoreType
This property denotes the type of the trust store. It takes a String value. Any valid trust store type supported by SSL can be assigned to this property. The default value is TrustStore.getDefaultValue().
javax.net.ssl.trustStorePassword
This property is used to set the password for the trust store. The trust store password is used to check the integrity of the data in the trust store before accessing it. The property takes a String value. It does not have any default value.
In the setup for your JMS stanza there is a field for entering these.
-Djavax.net.ssl.keyStore=somepath,-Djavax.net.ssl.keyStoreType=sometype, .......
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you for pointing the JVM Properties out. I was able to solve the issue with your suggestion.
When specifying the properties the following worked:
javax.net.ssl.keyStore=pathto\client.ks,javax.net.ssl.keyStorePassword=xxxxx,javax.net.ssl.trustStore=pathto\client.ts